Plant Sim
R&D development of machine learning software
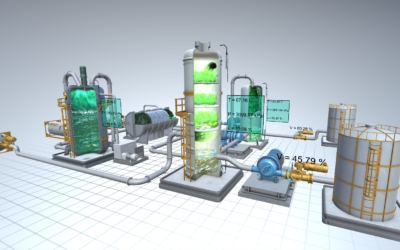
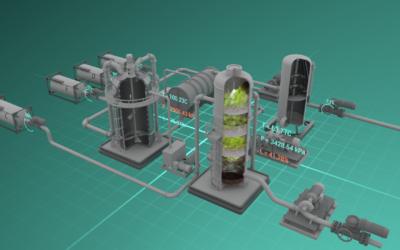
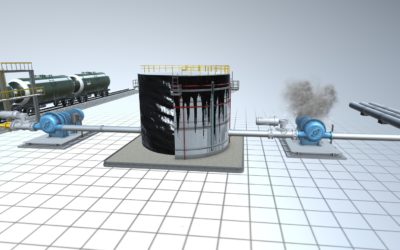
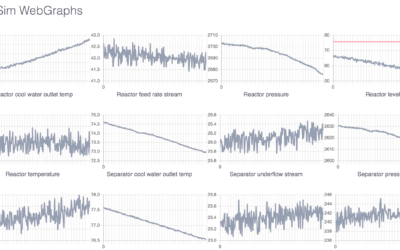
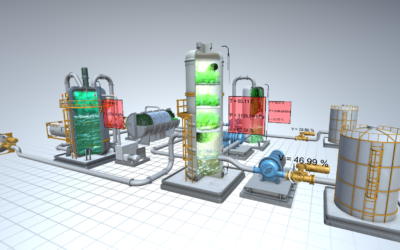
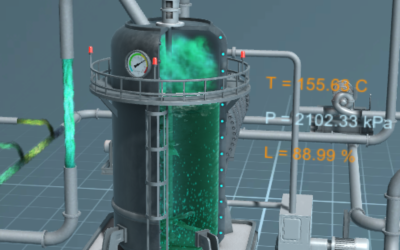
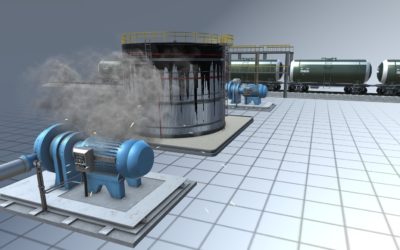
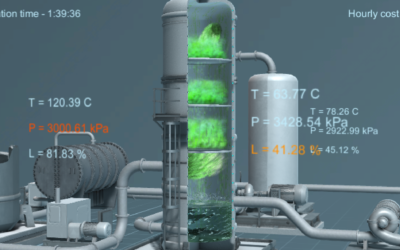
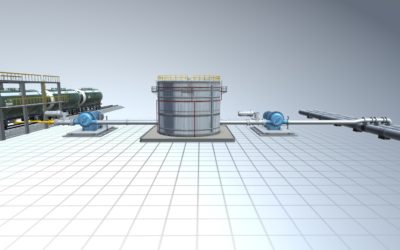
The project combines 3D visualisation technology, mathematical modelling and machine learning, which are paired with real industrial-grade equipment for dataset generation for later using to describe and detect any sorts of cyber-physical attacks on the facility.
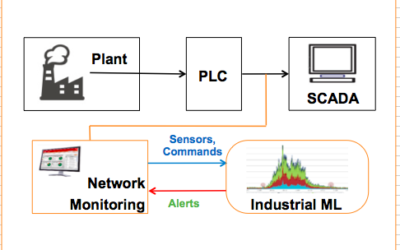
Using the Tennessee Eastman Process (simulational model was built on the Python language) and TANECO (implemented in OpenModelica), we built a PLC logic programme to control the physical model using the Unity engine. To illustrate simulated processes, we implemented 3D TEP/TANECO model and tied it to the generated physical model and PLC telemetry. To control the bench, a special iPad based console was developed. Through it you can simulate numerous cyber attack scenarios and simultaneously test MLAD algorithms.
Test bench was run on a single laptop – TEP, TANECO and 3D visualisation, Kaspersky Industrial Cyber-Security and MLAD were running on it. For the PLC we used a Scheinder controller. With a network switch the traffic between PLC and math model is mirrored to the Kaspersky Industrial Cyber-Security which later works with MALD.
*(MLAD – Machine Learning for Anomaly Detection – is a Kaspersky lab tech, which makes cyber attack detection easier and more efficient because of the implemented machine learning. This tech makes it possible to create another important layer of cyber defence and is usable for any attack patterns.)
Client: Kaspersky Lab
Year of the project implementation: 2017